PCI DSS vs ISO 27001: Key Differences Explained

Cybersecurity risks continue to grow every year. As a result, businesses face increasing pressure to protect their sensitive data and maintain customer trust. Sometimes you need to lock down specific payment details, while other times you need to secure your entire organization.
This leads many business leaders to compare PCI DSS and ISO 27001. If you operate a SaaS company, a fintech startup, a cloud provider, or an enterprise handling sensitive data, you might be wondering which path to take.
In this article, I will cover everything you need to know about both frameworks. We will look at their differences, scope, costs, and audit effort, helping you decide which option makes the most sense for your team.
What is PCI DSS?
The Payment Card Industry Data Security Standard (PCI DSS) is a set of security standards designed to help companies that accept, process, store, or transmit cardholder data maintain a secure environment.
The PCI Security Standards Council created this framework to protect cardholder data and reduce the risk of cardholder data compromise.
Who Needs PCI DSS
You may need to assess whether PCI DSS applies if your company works with payment card data. This involves:
Ecommerce companies
Payment processors
SaaS billing platforms
Fintech companies
PCI DSS Key Components
The framework is highly prescriptive, consisting of 12 core security requirements organized into 6 control objectives. These include building secure networks, protecting cardholder data, maintaining vulnerability management programs, implementing strong access controls, monitoring networks, and maintaining security policies.
With PCI DSS v4.0, the standard places greater emphasis on continuous compliance. Companies must understand that security is an ongoing requirement, not a one-time task.
What is ISO 27001?
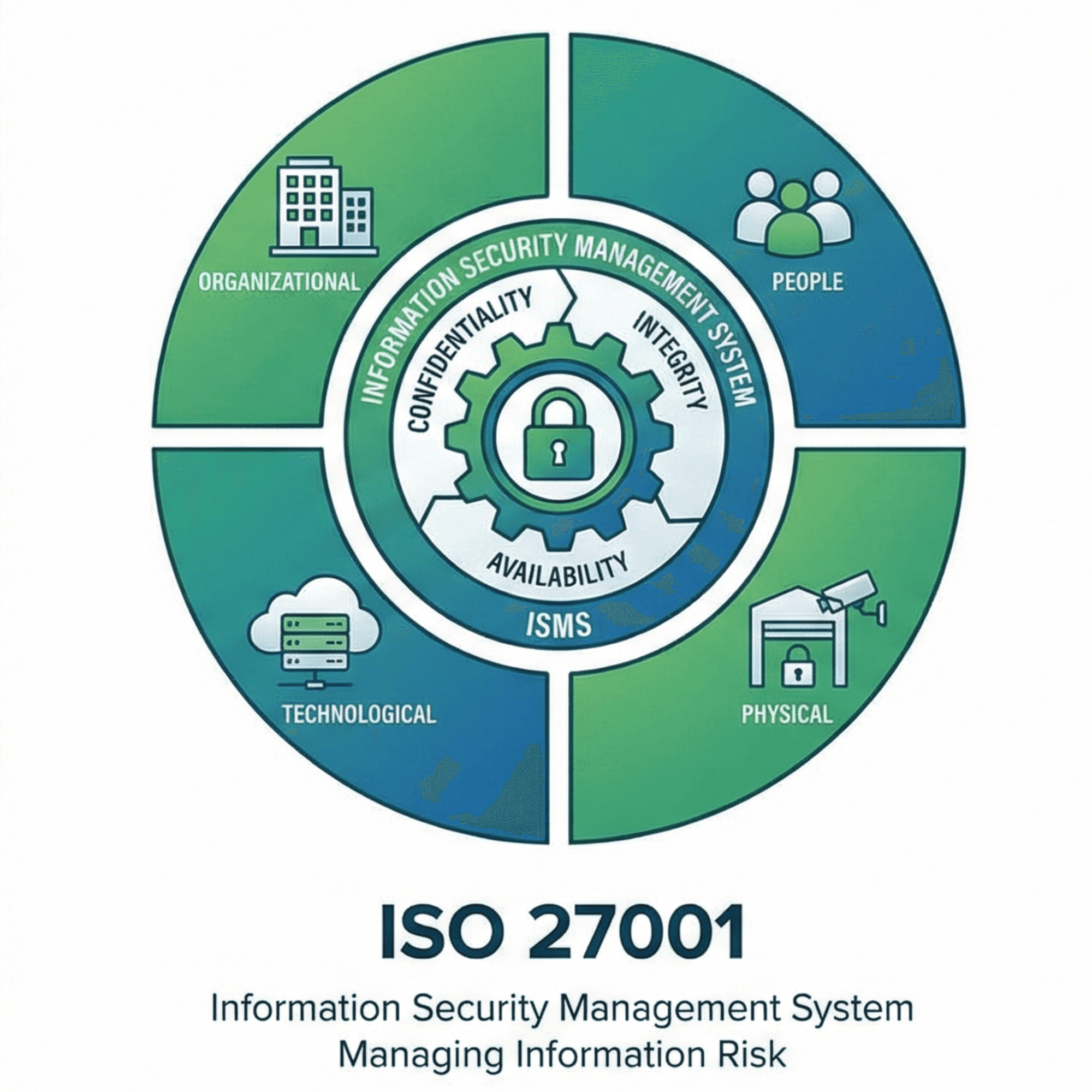
ISO 27001 is a globally recognized standard for information security. It defines the requirements for establishing, implementing, maintaining, and improving an Information Security Management System (ISMS).
In contrast to a list of technical requirements, ISO 27001 is a risk-based approach. It asks you to identify the specific security risks that threaten your data and to choose the appropriate controls to mitigate them.
Who Needs ISO 27001
Even though ISO 27001 is not mandatory, many B2B customers and partners commonly request it as part of security and vendor due diligence. This involves:
SaaS companies
Enterprises
Cloud providers
Technology startups
Managed service providers
ISO 27001 Key Components
A comprehensive ISO 27001 implementation begins with a risk assessment, after which organizations select applicable controls from the 93 controls in Annex A of ISO 27001:2022. A key aspect of ISO 27001 is its ongoing nature, rather than being a one-time certification. Instead, the continuous improvement cycle built into the standard will help ensure security activities remain relevant and effective in the face of changing threats, technologies, and business processes.
PCI DSS vs ISO 27001: Key Differences
While both frameworks aim to improve security, they take different approaches. Here is a quick comparison:
Feature | PCI DSS | ISO 27001 |
Purpose | Protect cardholder data | Establish a company-wide ISMS |
Scope | Cardholder Data Environment (CDE) and connected systems | Defined ISMS scope (can be entire company or selected scope) |
Mandatory vs Voluntary | Required by payment brands and acquiring banks for companies handling cardholder data | Voluntary, but often expected by enterprise clients |
Certification | Attestation of Compliance (AOC) / Report on Compliance (ROC) | Accredited certification by certification body |
Controls | 12 requirements and 300+ sub-requirements (PCI DSS v4.0) | 93 controls (ISO 27001:2022 Annex A) |
Industry Use | Payments and retail | Agnostic, used across all industries |
As you can see, PCI DSS provides prescriptive security requirements for protecting cardholder data. ISO 27001 provides a risk-based framework for managing information security risks across your entire business based on your unique needs.
PCI DSS vs ISO 27001: Scope Comparison
Understanding scope is the easiest way to see how these two standards diverge.
PCI DSS Scope: This standard focuses on the Cardholder Data Environment (CDE), which focuses on the people, processes, and technology that collect, process, and transmit cardholder data. It also includes the systems that are connected to or impact the security of cardholder data. Because of this, PCI scope is generally narrow but technically deep. This environment justifies very specific security requirements.
ISO 27001 Scope: This standard is related to a company's Information Security Management System (ISMS), which can be the whole company or some part of it, such as a specific product, service, or business unit. This scope is defined by the company and may cover the entire company or a defined business unit. It includes information assets, people, processes, and technologies relevant to the ISMS.
To use a simple analogy, PCI DSS is narrow but deep. It is like a high-security vault that has been built to store cash only. ISO 27001 is the opposite. It is broad and flexible and can be compared to an elaborate security system that is used to protect an entire office building.
PCI DSS vs ISO 27001: Requirements Comparison
The way you implement controls differs significantly between the two standards.
PCI DSS Requirements: There are 12 high-level requirements that have prescriptive controls attached to them. These requirements spell out specific criteria like how firewalls should be configured, what the password policy should be, how encryption and vulnerability management should be done, etc.
ISO 27001 Requirements: Your company’s unique risk assessment determines which controls in Annex A apply. ISO 27001 defines control objectives while allowing companies flexibility in selecting appropriate controls.
Area | PCI DSS | ISO 27001 |
Access control | Strict, mandatory rules for system access | Risk-based access control policies |
Encryption | Highly specific cryptographic requirements | Applied based on data sensitivity |
Monitoring | Mandatory logging and vulnerability scanning | Monitoring based on ISMS risk and control objectives |
Policies | Specific policies tied to the 12 requirements | Broad, company-wide security policies |
Risk management | Limited risk-based flexibility (PCI DSS v4.0 customized approach) | Core foundation of the ISMS |
PCI DSS vs ISO 27001: Certification Process
Both frameworks are significantly different when it comes to first achieving compliance.
PCI DSS Certification Process:
Scope definition (Cardholder Data Environment identification)
Gap assessment against PCI DSS requirements
Remediation of identified gaps
Security testing (vulnerability scans, penetration testing)
Assessment by Qualified Security Assessor (QSA) or Self-Assessment Questionnaire (SAQ)
Issuance of a Report on Compliance (ROC) and Attestation of Compliance (AOC) (for Level 1 merchants/service providers), or Self-Assessment Questionnaire (SAQ) and AOC (for smaller companies)
ISO 27001 Certification Process:
Define ISMS scope
Conduct risk assessment and risk treatment plan
Implement security controls
Internal audit
Management review
Stage 1 audit (documentation and readiness review)
Stage 2 audit (implementation and effectiveness review)
Certification issuance by accredited certification body
PCI DSS vs ISO 27001: Audit Stages and Effort
Audits can be stressful, but knowing what to expect helps you prepare.
PCI DSS Audit: Depending on your transaction volume and merchant classification, you might complete a Self-Assessment Questionnaire (SAQ) or need a full assessment by a Qualified Security Assessor (QSA). This validation is an annual requirement, often accompanied by necessary vulnerability scans and penetration tests.
ISO 27001 Audit: Getting certified requires a Stage 1 and Stage 2 audit by an external body. After certification, you will undergo smaller annual surveillance audits and a recertification audit every three years.
Audit Factor | PCI DSS | ISO 27001 |
Audit frequency | Annual validation | 3-year certification cycle with annual surveillance |
Audit complexity | Highly technical and control-focused | Governance, risk, and control effectiveness |
Documentation effort | Technical evidence, logs, configurations | Policies, risk assessments, governance documentation |
Timeline | Varies widely based on CDE size and complexity | Typically 6 to 12 months for initial certification |
PCI DSS vs ISO 27001: Cost Comparison
Planning a budget to meet compliance needs to address several factors.
PCI DSS Cost Factors: Cost is a function of the complexity of your Cardholder Data Environment (CDE), your merchant/service provider level, the type of audit you require (e.g., SAQ and full assessment by a QSA), and whether or not you need any remediation to meet particular technical controls.
ISO 27001 Cost Factors: Costs for ISO 27001 are shaped by the scope of your ISMS, the size of your company, the level of maturity of your implementation, and the costs of the certifying body. You may also need to budget the costs of additional activities like risk assessments, documentation, and internal audits.
Cost Area | PCI DSS | ISO 27001 |
Consulting | Scoping, technical readiness, remediation guidance | Gap assessment, ISMS design, risk framework implementation |
Audit | QSA assessment, ASV scans, penetration testing | Stage 1, Stage 2, and surveillance audit fees |
Maintenance | Continuous compliance and logging tools | Ongoing risk assessments and internal audits |
Tools | Network security and encryption software | Governance, risk, and compliance platforms |
PCI DSS vs ISO 27001: Similarities
In most ways, PCI DSS and ISO 27001 differ from one another. Both, however, have several common features. Both PCI DSS and ISO 27001 are widely adopted security frameworks with well-documented security governance and risk management practices.
Both frameworks generally require:
Security policies and procedures
Risk identification and mitigation
Regular assessments or audits
Ongoing monitoring and maintenance
Implementing PCI DSS or ISO 27001 can demonstrate structured security governance and risk management practices, which may strengthen customer trust and assurance.
Do You Need PCI DSS or ISO 27001?
Choosing between PCI DSS or ISO 27001 is determined by your business model, your customers’ needs, and the data you collect.
Choose PCI DSS If:
Your company processes, stores, or transmits cardholder data.
Your company deals with payment systems or payment platforms.
Your company has PCI DSS validation requirements set by payment brands or acquiring banks.
Choose ISO 27001 If:
You have enterprise customers with security requirements.
You want security information and documentation for the entire company.
You have sensitive customer or company data.
Choose Both If:
You are a fintech company that deals with payment data and customer information.
You are a SaaS company that has integrated payment functionality.
You provide cloud platforms that also have payment and sensitive enterprise data.
How Roz Simplifies PCI DSS and ISO 27001 Audit Readiness
Preparing for PCI DSS and ISO 27001 audits can involve significant documentation, control mapping, and review workflows. Our tool helps CPA firms and advisory teams streamline audit readiness with structured, AI-assisted engagement delivery.
Roz helps teams:
Generate AI-assisted draft workpapers with audit trails
Extract and map controls from uploaded documentation
Organize evidence in centralized client workspaces
Highlight documentation gaps through first-pass analysis
By structuring documentation and analysis, Roz helps teams prepare for PCI DSS and ISO 27001 engagements more efficiently while reducing manual effort.
Conclusion
To build a secure business, you need the right tools for the job. PCI DSS applies specific technical security requirements to very specific payment data, while ISO 27001 provides a company-wide, risk-based framework for managing information security. Due to the differing scopes of these frameworks, many developing companies implement both.
Your business model, the data you collect, and the needs of your customers will impact which framework you need to prioritize. From these, your company will develop the right security practices and will be able to manage information security risks and the complexity of managing highly sensitive data as your company grows.
I hope you have learned key differences you need to know about PCI DSS and ISO 27001.