What is SOC 2 Compliance? A Beginner's Guide

What is SOC 2 Compliance? A Beginner's Guide
SOC 2 compliance has become a widely recognized benchmark for demonstrating data security and operational maturity to customers, investors, and partners. For organizations handling sensitive customer data, especially SaaS companies, cloud providers, and service companies, it's often a key requirement in enterprise procurement processes.
But what exactly is SOC 2? How does it work? And how can your organization achieve compliance without drowning in spreadsheets and manual processes?
In this article, I will break down everything you need to know about SOC 2 compliance, from the fundamentals to practical steps involved in preparing for a SOC 2 audit.
What Does SOC 2 Mean?
SOC 2 (System and Organization Controls 2) is an attestation framework developed by the AICPA and focuses on the protection of consumer data based on specific Trust Services Criteria. Although SOC 2 is voluntary, it is becoming more common among enterprise clients, investors, and partners. Furthermore, it is voluntary, is not a one-time achievement, and is an independent attestation report from a government-issued certified public accountant firm that evaluates the company's controls.
This type of certification is especially relevant to SaaS, cloud, fintech, and healthtech service providers that deal with sensitive data.
Companies choose the relevant Trust Services Criteria and then have an audit conducted on them to confirm compliance. This, in turn, shows a level of maturity regarding security, and the company is then able to build confidence with the stakeholders.
What is SOC 2 Compliance?
SOC 2 compliance means that a company has taken the necessary steps to implement and uphold the security controls that align with the Trust Services Criteria and has also undergone an independent audit to confirm such actions.
What is different about SOC 2 is that it does not implement a checkbox-type system. Instead, it is done through a risk-based framework, which encourages companies to focus on their individual risks and tailor the framework and controls to meet those specific needs.
The flexibility involved here means that not every SOC 2 report looks the same. Take, for example, a cloud infrastructure provider. They may emphasize the controls they have in place for availability. In contrast, a healthcare provider of software-as-a-service solutions may discuss the importance of privacy and confidentiality in their report.
The audit verifies three things:
Controls are properly designed to meet relevant Trust Services Criteria.
Controls are implemented as described.
Controls operate effectively over time (for Type 2 reports).
What Is a SOC 2 Audit?
A SOC 2 audit is a review done by independent auditors from a CPA firm. The auditors review if the company’s security controls meet specific standards for design (Type 1 and Type 2), implementation (Type 2), and operation effectiveness over time (Type 2).
The audit process includes:
Evidence-based testing of security control.
Interviews of key personnel.
Reviews of different policies, processes, and other relevant documentation.
Observing the system to verify security control.
After the audit, you will receive a SOC 2 report to explain the systems, controls, and the auditor’s evaluation of the effectiveness.
Types of Auditor Opinions
The auditor's opinion falls into one of four categories:
Unqualified (Clean Opinion): All controls effectively meet SOC 2 criteria.
Qualified: Some controls are acceptable, but other areas need to be improved.
Adverse: Some controls are significantly deficient.
Disclaimer of Opinion: Not enough information to support a conclusion.
What Is a SOC 2 Report?
A SOC 2 report is the documentation of your audit and describes your security posture, which includes:
Management's Assertion: Your company claims that the controls are aligned with the established criteria.
System Description: A detailed description of the systems and services that were covered by the audit.
Auditor's Opinion: Assessing your control framework is based on their independent judgment.
Control Details and Test Results: Results of specific control tests. The control description is part of a Type 1 report, and a Type 2 report goes further by providing specific test descriptions and outcomes that show continued operational effectiveness.
Exceptions (if any): Any controls that failed or deficiencies that were discovered during the audit.
Customers, partners, and stakeholders who require verification of your security practices share confidential SOC 2 reports under NDA.
SOC 2 Type 1 vs. SOC 2 Type 2 - What's the Difference?
When it comes to SOC 2 reports, Type 1 and Type 2 are two different types that are critical to understanding.
Aspect | Type 1 | Type 2 |
Timeframe | Point-in-time | Defined review period (typically 6–12 months) |
What It Tests | Design of controls | Design and operating effectiveness |
Timeline | Faster (2-4 months) | Longer (6-12+ months) |
Customer Preference | Less trusted | More trusted |
Use Case | Early-stage validation | Enterprise readiness |
A Type 1 report provides an overview of your controls and evaluates their design based on a specific date. It won’t state whether these controls functioned and operated as designed over a period of time, but Type 1 reports are useful for growing companies to identify and show potential and provide a place to document historical controls prior to a Type 2 review.
A Type 2 report analyzes and assesses controls over a period of time, typically 6 to 12 months, and measures both the design and operating effectiveness of controls. This means that auditors assess not only whether the controls are designed properly but also whether they functioned as intended throughout the entire review period.
This sustained performance makes Type 2 reports the preferred choice for enterprise customers and procurement teams.
Who Needs SOC 2 Compliance?
Companies that handle customers' personal data (storage, processing, or transmitting) should consider SOC 2 compliance. This includes:
SaaS companies
Cloud service and managed service providers
Fintech platforms
Healthcare technology companies
Data analytics and AI platforms
Although your industry doesn't require it, SOC 2 compliance can help you:
Win enterprise deals by meeting vendor security requirements
Stand out from the competition
Reduce time spent on security questionnaires
Build customer trust through third-party validation
Strengthen your internal security posture
The 5 SOC 2 Trust Services Criteria Explained
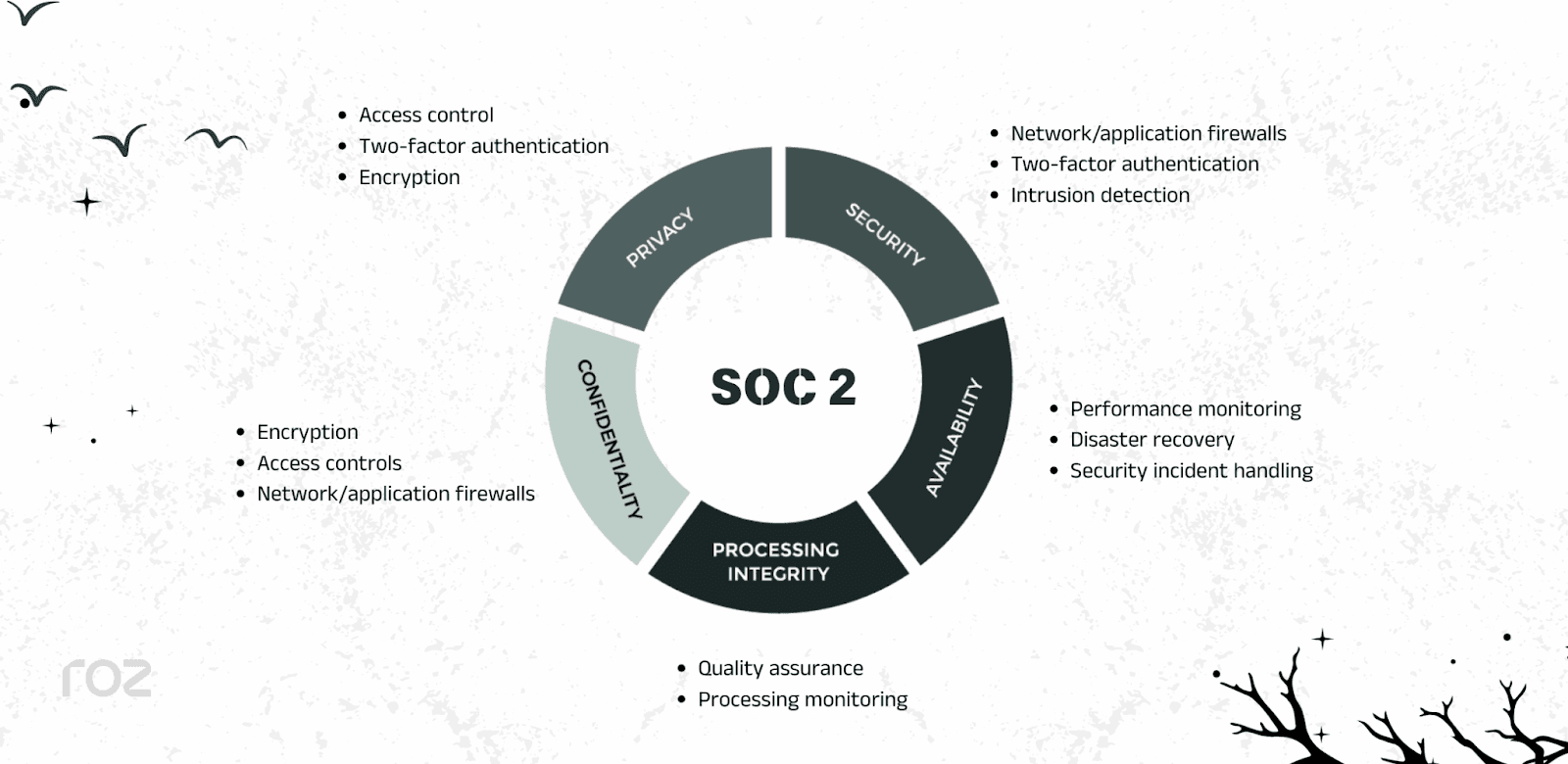
SOC 2 does not provide a prescriptive checklist of controls. Instead, it is based on five Trust Services Criteria defined by the American Institute of Certified Public Accountants. These criteria guide how organizations design and evaluate their control environment. All SOC 2 examinations include security. The other criteria are included based on the services provided and risks identified.
1. Security (Mandatory)
The security criteria, also called "Common Criteria," are required for all SOC 2 audits. They focus on protecting systems from unauthorized access, breaches, and misuse.
Control examples:
Logical and physical access controls
Access management and authentication
Change management processes
Risk assessment and mitigation
Incident response procedures
System monitoring and logging
Vulnerability management
Network security controls
Vendor and third-party risk management
2. Availability
The availability criteria ensure that systems are operational and accessible as agreed upon in commitments like service-level agreements (SLAs). This focuses on the controls that support operational resilience, rather than just uptime guarantees.
Control examples:
Business continuity planning
Disaster recovery planning and testing
System performance monitoring
Capacity planning
Backup and restoration procedures
Infrastructure redundancy
3. Processing Integrity
The Processing Integrity criteria evaluate whether systems process data accurately, completely, in a timely manner, and with proper authorization.
Control examples:
Data validation checks
Error detection and correction procedures
Transaction monitoring
Quality assurance and review processes
Reconciliation procedures
4. Confidentiality
It safeguards confidential company information from unauthorized access or disclosure.
Control examples:
Data encryption (in transit and at rest)
Non-disclosure agreements
Confidential data classification
Secure disposal procedures
5. Privacy
The privacy criteria focus on personal information, assessing whether it is collected, used, retained, disclosed, and disposed of in alignment with the organization’s privacy commitments.
Control examples:
Privacy policy documentation
Notice and consent mechanisms
Data minimization practices
Third-party data sharing controls
Data retention schedules
Data subject rights procedures
Privacy incident response processes
How Long Does It Take to Get SOC 2?
Your company's structure can determine the timeline.
For companies starting from scratch, they would have timelines varying from
Readiness phase: 1-3 months to implement controls and policies
Observation period (Type 2): 6-12 months of control operation.
Audit fieldwork: 4-8 weeks
Report issuance: 2-4 weeks
Total timeline: 6-15 months for Type 2 compliance
For companies with existing security programs:
Many policies and processes may already meet Trust Services Criteria.
The readiness phase may be shorter (4-8 weeks).
For a Type 2 examination, an observation period of 6 to 12 months is still required.
In these cases, the total timeline may be reduced, but the observation period cannot be skipped.
Factors that affect timeline:
The first factor to consider is your current level of security maturity.
The level of documentation is already in place.
Your team's availability and the company's ownership are crucial factors in achieving this.
The complexity of your systems and infrastructure is a key consideration.
The number of Trust Services Criteria you are considering.
The extent to which you rely on subservice companies is also a crucial factor.
How Roz Accelerates SOC 2 Engagement Delivery
SOC 2 engagements require structured documentation, evidence mapping, and rigorous testing. For CPA firms and advisory teams, the manual work involved; drafting workpapers, extracting controls, organizing evidence, and documenting findings; can consume hundreds of hours per engagement.
We are an AI-native audit delivery platform built for CPA, risk assurance, and advisory teams performing control-based engagements.
Roz supports SOC 2 workflows by:
Automating first-pass evidence organization from uploaded client documents
Extracting documented controls and mapping them to Trust Services Criteria
Performing structured gap analysis before detailed testing begins
Conducting first-pass control testing and evidence sufficiency checks
Generating draft workpapers with full audit trails and source traceability
By replacing spreadsheet-heavy processes with structured AI-assisted workflows, companies can improve engagement consistency, increase margin, and scale delivery capacity without increasing headcount.
Book a demo to see how Roz accelerates SOC 2 engagements.
Conclusion
For many companies trying to sell to enterprise companies, SOC 2 is becoming increasingly relevant, as it is a powerful way to show trust to potential buyers, make selling to them easier, and show the buyer the operational maturity of the enterprise.
To succeed, start as early as you can, document your processes and build controls that are sustainable, and use the right technology, especially automation, to take the load off your team.
No matter if you’re just starting out on your compliance journey or you’re optimizing repeat audit cycles, companies that view compliance as a long-term capability (rather than a one-time obligation) are more likely to be positioned for long-term scalable growth and competitive advantage in more security-focused marketplaces.
Want to improve your SOC 2 engagements? See how our tool streamlines audit delivery with structured, AI-assisted workflows.