NIST SP 800-53 Rev. 5: A Complete Guide for Compliance Teams

Managing third-party risks and securing cloud environments can be a challenging task. As organizations shift more operations to the cloud, the attack surface expands, making standardized control frameworks increasingly important. Without a standard approach to security, organizations may lack a structured method for determining appropriate security controls to protect their systems.
This is where the National Institute of Standards and Technology (NIST) comes in. NIST provides guidance for building and managing secure information systems. Within their library of publications, NIST Special Publication (SP) 800-53 stands out as one of the most comprehensive catalogs of security and privacy controls available globally.
NIST 800-53 is not a certification you can frame and hang on a wall. Instead, it is a foundational catalog used for risk-based control selection. If you are an auditor, CISO, or compliance team member, this framework helps you build a defensible, standardized security posture.
In this article, you will understand the structure of the Rev. 5 catalog, how to implement its baselines, and how to use a basic checklist to get started.
What is NIST SP 800-53 Rev. 5?
NIST SP 800-53 Rev. 5 is one of many publications developed by the National Institute of Standards and Technology. It provides a comprehensive catalog of security and privacy controls that organizations can use to support risk management, align with regulatory expectations, and protect information systems.
NIST SP 800-53 is used by both public and private sector organizations, including industries such as healthcare and higher education. It is closely associated with the Federal Information Security Modernization Act (FISMA), which requires federal agencies to implement and maintain an organization-wide information security program based on documented risk management practices.
From an auditing perspective, NIST 800-53 offers two primary advantages:
Standardized Approach: This framework allows organizations to articulate their security standards using a consistent and standardized language.
Evidence-based assurance: Evidence-based assurance: This framework outlines controls that support compliance efforts, enabling auditors to assess how controls align with defined requirements.
Structure of NIST 800-53 Rev. 5
Understanding how the catalog is organized is the first step toward using it effectively. The framework is massive, but it follows a logical hierarchy.
Control Families Overview
The control catalog consists of 20 families. The domain of each control as it relates to security and privacy is denoted by a two-letter code. Below is a partial NIST 800-53 control family listing.
Access Control (AC): Control family that outlines requirements for access to information systems.
Incident Response (IR): Control family assists establishments in preparing for and responding to a security incident.
System and Information Integrity (SI): Controls implemented to protect systems from defects and malicious software.
Supply Chain Risk Management (SR): A more recent family focused on the management of risks from third-party suppliers.
Control Statements
Each family consists of several control statements. A control statement refers to the obligation that you need to satisfy (for example, “The organization develops and documents an access control policy”). A control statement differs from supplemental guidance, which only provides an example or context for the control you are trying to implement.
Privacy Integration
In previous editions, privacy was situated in the final sections and was largely overlooked. Rev. 5 incorporates privacy into every control in the entire catalog. Such consolidation means that organizations need to integrate and implement protective measures for both data protection and data privacy.
Controls vs Control Enhancements
Not all systems require the same level of protection. To account for this, NIST uses a structure of base controls and control enhancements.
Base Controls: The fundamental, minimum expectations for a specific security capability.
Control Enhancements: Additional, more rigorous requirements added to a base control to protect systems with higher risk levels.
For example:
AC-2: The base control for account management. It requires you to define and manage system accounts.
AC-2(1): An enhancement that specifically requires automated system account management.
Feature | Base Control | Control Enhancement |
Purpose | Establishes the foundational security requirement. | Adds specific rigor or advanced capabilities. |
Example | AC-2 (Account Management) | AC-2(1) (Automated System Account Management) |
Audit Implication | Expected for most standard baselines. | Typically required for high-impact or critical systems; not optional if selected in your baseline. |
If you manage high-risk systems, enhancements are not optional suggestions. They are required when included in the selected baseline and are typically subject to audit evaluation.
Baselines (Low, Moderate, High)
Instead of expecting every enterprise to apply all 1,196 controls, NIST applies the principle of baselines. NIST defines a baseline as a predefined set of controls corresponding to a specified risk level. The risk level for your baseline is established using Federal Information Processing Standards (FIPS) 199, which sorts systems relative to the potential risk to the organization through a system breach.
Low Baseline
This baseline applies to systems where a breach results in minimal to no adverse effect on the organization, the loss of property or assets, or limited adverse impact on organizational operations, assets, or individuals. It is predominantly foundational in nature, and it is comprised of around 149 controls.
Moderate Baseline
A breach in this system could result in financial loss or disruption of service to a degree that becomes significant in virtually all enterprise systems and federal systems. This baseline includes around 287 controls and is the baseline for a significant number of FedRAMP authorizations.
High Baseline
This baseline is for critical infrastructure or classified systems that contain significant or sensitive data. A breach of a high-impact system would be both potentially catastrophic and life-threatening. It requires the most extensive set of controls, which is around 370 controls.
NIST 800-53 Baselines Overview
Overview
Baseline | Controls Volume | Use Case |
Low | ~149 Controls | Minimal impact systems, public-facing data. |
Moderate | ~287 Controls | Most enterprise systems are standard FedRAMP workloads. |
High | ~370 Controls | Critical infrastructure, highly sensitive or classified data. |
How NIST 800-53 Fits into the RMF
It is important to understand that NIST 800-53 is a control catalog, not a standalone framework. To actually implement these controls, federal agencies use the NIST Risk Management Framework (RMF), outlined in NIST SP 800-37.
RMF Steps Breakdown
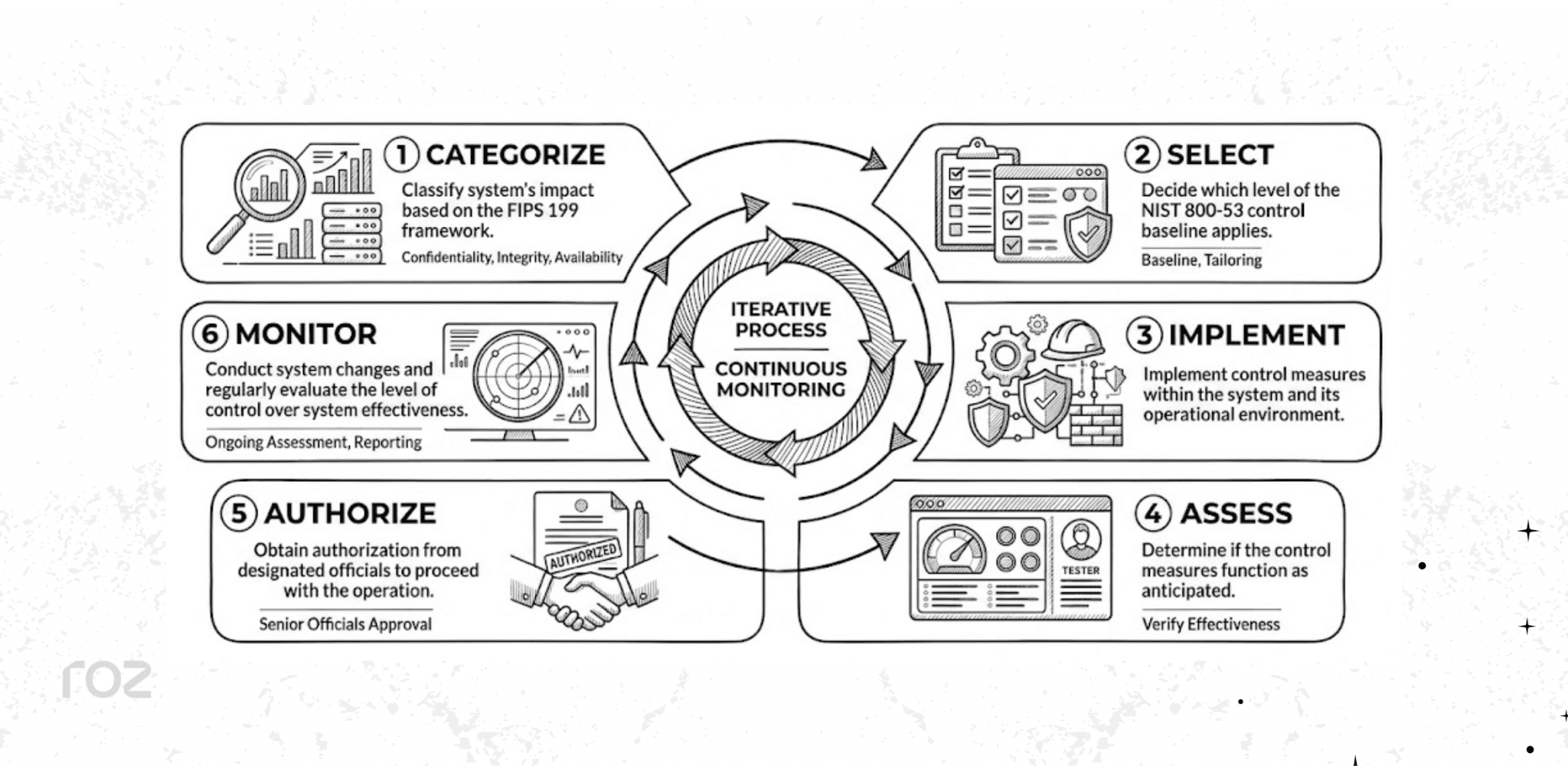
RMF consists of 6 steps to help manage system risks. Here is a simple breakdown of each step.
Categorize: Classify the system's impact based on the FIPS 199 framework.
Select: Decide which level of the NIST 800-53 control baseline applies.
Implement: Implement control measures within the system and its operational environment.
Assess: Determine if the control measures function as anticipated.
Authorize: Obtain authorization from designated officials to proceed with the operation.
Monitor: Conduct system changes and regularly evaluate the level of control over system effectiveness.
Key Changes in Rev. 5 (What’s New)
There are multiple catalog updates in Rev. 5. For those used to older frameworks, this update will be a big change.
Security + Privacy Integration
As mentioned earlier, privacy controls are no longer separate in Appendix J. These controls are integrated into the primary control families, which reflects that security and privacy are essential to each other.
New Control Families (SR, PT)
Rev. 5 added two family categories. SR focuses on supply chain risk management, while PT (Personally Identifiable Information Processing and Transparency) addresses privacy-related requirements.
Outcome-Based Controls
Rev. 5 took a large leap to address the outcomes of the control rather than the framework tools. This approach allows companies to control the outcomes of the Rev. 5 while dictating their framework.
Removal of “Federal-only” Positioning
Rev. 5 reduces federal-specific language and explicitly broadens applicability to the private sector and non-government organizations, while still supporting federal compliance requirements.
Support for cloud, IoT, DevSecOps
The updated, agnostic vernacular simplifies the application of these rules to modern systems, like multi-cloud infrastructures, IoT, and rapid DevSecOps.
Rev. 4 vs Rev. 5 Key Differences
Feature | Rev. 4 | Rev. 5 |
Privacy Controls | Segregated in Appendix J | Integrated throughout the catalog |
Control Families | 18 Families | 20 Families (Added SR and PT) |
Language Focus | System-centric, federal focus | Outcome-based, technology-neutral, universal focus |
Baseline's Location | Included in the main document | Baselines were separated into NIST SP 800-53B |
How to Implement NIST 800-53 Rev. 5
Implementation can feel overwhelming, but breaking it down into structured steps makes the process manageable.
Define System Scope: Clearly map out the boundaries of the information system. Identify all hardware, software, data flows, and network connections involved.
Categorize (FIPS 199): Determine the potential impact of a breach (low, moderate, or high) across confidentiality, integrity, and availability.
Select Baseline: Use NIST SP 800-53B to select the starting baseline that corresponds to your FIPS 199 categorization.
Tailor Controls: You do not have to blindly accept the baseline. Tailor the controls to your specific environment by scoping out irrelevant requirements or adding compensating controls.
Implement Controls: Document your policies, configure your systems, and put the required security measures into practice.
Perform Assessment: Conduct internal testing or hire a third party to verify that the controls are designed and operating effectively. Auditor review patterns frequently focus on how well your written policies match your actual system configurations.
Continuous Monitoring: Security is not a one-time project. Set up mechanisms to continuously monitor your controls, update documentation, and gather evidence of ongoing compliance.
NIST 800-53 Controls Checklist
To help you prioritize and establish a framework to organize your efforts, a high-level foundation control checklist has been devised. This list is not comprehensive and should be tailored to your framework and the specific baseline.
Access Control: Implement unique user identification and multi-factor authentication.
Logging & Monitoring: Verify that system logs are storing security events and confirm that alerts for suspicious activity are set up.
Incident Response: Design and practice employee roles and communication steps for containment to ensure the incident response plan is documented and tested.
Vendor Risk: Develop a method to evaluate the security strength of third-party suppliers prior to allowing them to access your information.
Use this checklist as a starting point and not a replacement for a structured risk evaluation.
Common Implementation Challenges
Transitioning to NIST 800-53 is rarely simple. Teams typically run into a few predictable roadblocks.
Overwhelming Control Volume
With over 1,000 controls and enhancements, organizations often try to implement everything at once. This leads to inefficiencies and implementation challenges. You should focus strictly on your tailored baseline.
Lack of Clear Ownership
If no single person is accountable for a specific control family, that area will likely fail an audit. Assign clear owners for policies, implementation, and evidence collection.
Evidence Collection Gaps
Most audit failures occur in control testing, not implementation. Teams often build great security mechanisms but fail to generate the logs, screenshots, or reports required to prove it to an auditor.
Misinterpreting Control Intent
Because the language is outcome-based, teams sometimes struggle to translate a requirement into a technical setting. Always read the supplemental guidance provided by NIST to understand the intent.
Mapping to Other Frameworks
If you are also pursuing SOC 2 or ISO 27001, managing overlapping controls in spreadsheets quickly becomes chaotic. Cross-mapping manually is highly prone to human error.
How Roz Supports NIST SP 800-53 Rev. 5 Engagements
Managing documentation, evidence, and control mapping for a NIST SP 800-53 Rev. 5 engagement can be time-consuming for advisory teams. Roz is an AI-native engagement and audit-delivery platform that supports CPA firms and advisory teams by acting as an intelligent enterprise data room.
Roz does not replace auditors or certification processes. Instead, it supports audit workflows and documentation through several key capabilities:
Centralized documentation workspaces for policies and evidence.
Control extraction and mapping from uploaded documentation.
Gap identification through first-pass analysis.
AI-assisted draft workpapers with audit trails and source links.
Roz supports audit workflows and documentation without replacing auditors, helping teams manage engagements more efficiently and with better traceability.
Conclusion
NIST 800-53 Rev. 5 is a foundational control catalog that reflects a shift toward modern risk management practices by integrating privacy and removing outdated, technology-specific constraints. By tailoring the controls to fit your specific risk profile, you can build a highly defensible security posture that stands up to rigorous audits.
As the regulatory landscape shifts and cloud ecosystems grow more complex, the relevance of standardized frameworks like NIST 800-53 will only increase. Adopting these practices today can support your organization's resilience tomorrow.
FAQ
What is NIST SP 800-53 Rev. 5 used for?
NIST SP 800-53 Rev. 5 provides a comprehensive catalog of security and privacy controls for information systems. Organizations use it to select controls that address identified risks, protect data, and support compliance efforts such as FISMA and FedRAMP.
How many controls are in NIST 800-53?
The Rev. 5 catalog includes 1,196 controls and control enhancements, organized across 20 control families.
Is NIST 800-53 mandatory?
NIST SP 800-53 is mandatory for U.S. federal agencies under the Federal Information Security Modernization Act (FISMA). It is also commonly required for cloud service providers pursuing FedRAMP authorization. For private sector organizations, it is generally voluntary but widely adopted as a best practice.
What is the difference between NIST 800-53 and the NIST Cybersecurity Framework (CSF)?
The NIST Cybersecurity Framework (CSF) is a high-level framework that organizes cybersecurity activities into core functions (Identify, Protect, Detect, Respond, and Recover). NIST SP 800-53 provides a detailed catalog of security and privacy controls that organizations can implement to support those functions.