ISO 27002 Controls Explained: A Complete Guide for Auditors

Why are compliance teams and security leaders paying closer attention to ISO/IEC 27002? It often reflects a broader shift from static, checklist-based compliance toward more dynamic, risk-based control frameworks.
As cyber threats continue to evolve, information security management typically requires more than passing a point-in-time audit. It involves a structured approach to selecting, implementing, and evaluating controls. For auditors, compliance teams, and security leaders, a clear understanding of ISO 27002 can support more effective risk management and more consistent audit outcomes.
In this article, I explain ISO 27002 controls from an audit and implementation perspective, rather than focusing solely on theory.
What ISO 27002 Actually Is (and What It Isn’t)
A common challenge for organizations is understanding the purpose of ISO 27002 and how it is intended to be used.
What it is:
A control implementation guide: It provides detailed advice on how to implement security controls.
A supporting standard: It acts as a companion to ISO/IEC 27001.
A risk treatment reference: It provides a set of recommended practices that can be selected based on your specific risk assessment.
What it is NOT:
Not certifiable: Organizations cannot be certified against ISO 27002.
Not mandatory by itself: It is not a regulatory requirement; however, it is commonly used as the primary reference for implementing controls selected under ISO 27001.
Not a checklist-only framework: Implementing every control without considering your risk profile may lead to unnecessary complexity and inefficient allocation of resources.
Common Misconception: Many organizations mistakenly believe they must implement every control listed in ISO 27002. This is incorrect. You only need to apply the controls that address the specific risks identified in your risk assessment. Your choices, both inclusions and exclusions, are documented in a Statement of Applicability (SoA) with justifications for each.
How It Fits with ISO 27001
To understand ISO 27002, it is important to first understand ISO 27001.
ISO 27001 Annex A offers a reference set of controls, and ISO 27002 explains, in detail, how to implement and customize those controls. Information security management system (ISMS) processes commonly follow this path:
Risk Assessment: You identify a specific security risk.
Control Selection: You select a control from ISO 27001 Annex A to treat that risk.
Implementation: You use ISO 27002 to understand the best practices for applying that control.
Audit: An auditor evaluates whether the control is designed and operating effectively.
ISO 27002 supports implementation depth. It provides the "how-to" guidance that brings the high-level requirements of ISO 27001 to life.
Inside the Four Control Themes
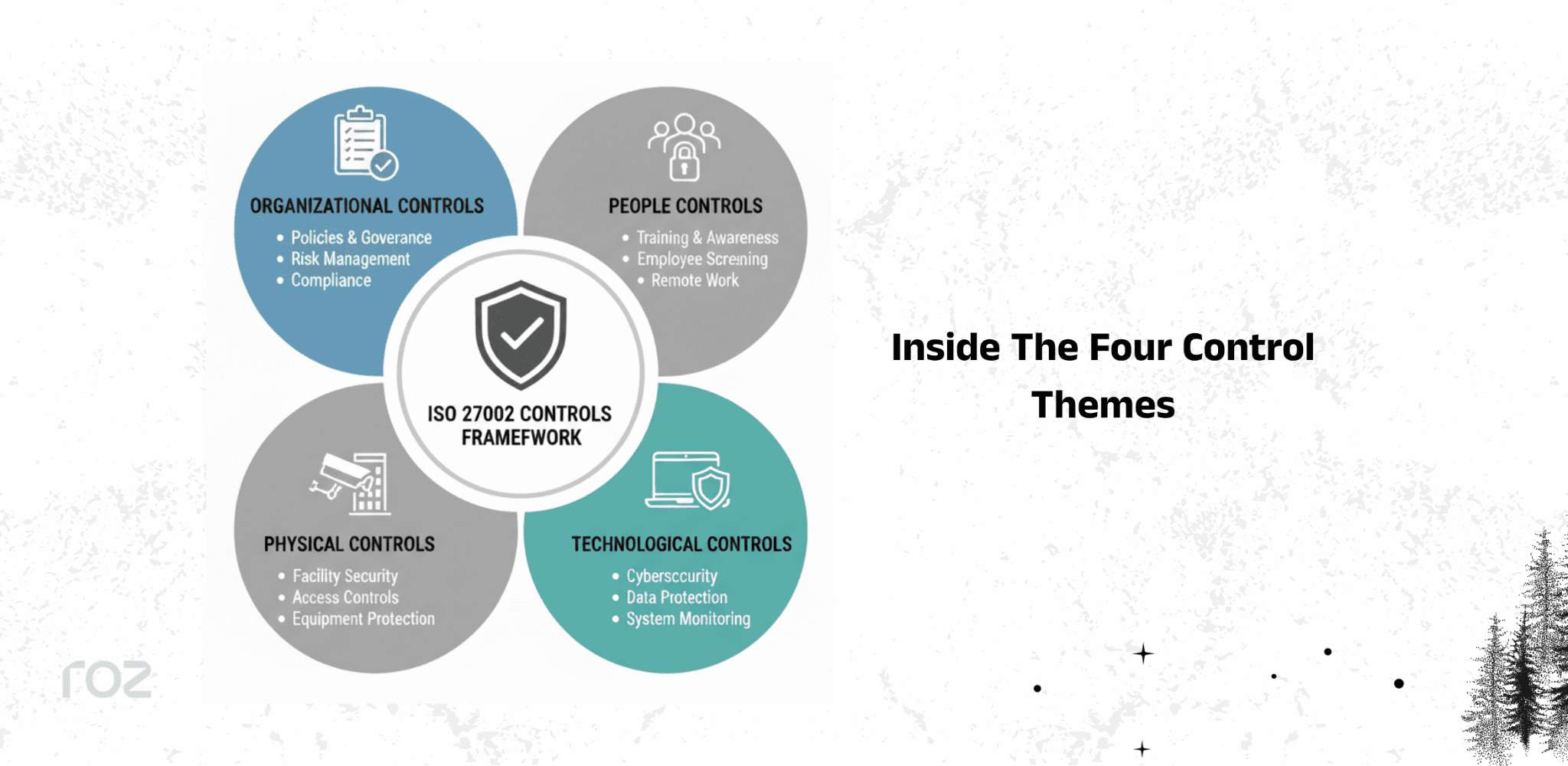
The 2022 update of ISO 27002 has reorganized controls into a four-theme structure. This is likely to help ease control organization and, in turn, promote improved ownership and management of compliance tasks.
Organizational Controls (Clause 5)
These 37 controls deal with governance, policies, and the overall management framework of information security.
Examples: Information security policies, threat intelligence, cloud services security
What this means in practice: Organizations are expected to appropriately implement a governance framework that is clearly defined, approved, and consistently enforced by leadership.
People Controls (Clause 6)
These 8 controls deal with human-related risks of information security.
Examples: Screening, training, awareness, and remote working
What this means in practice: Organizations have an ongoing duty to manage people risk in all phases of employment, including how they onboard, change roles, and terminate employees.
Physical Controls (Clause 7)
These 14 controls pertain to the protection of physical environments, facilities, and equipment.
Examples: Physical security perimeters, secure areas, equipment protection
What this means in practice: Organizations are expected to have controls that reduce the risk of unauthorized physical access and minimize the impact of environmental threats, such as fire, power loss, disruptive equipment, etc.
Technological Controls (Clause 8)
These 34 controls are the largest category and focus on technological safeguards in the area of IT systems and infrastructure.
Examples: Access control, data leakage prevention, secure coding
What this means in practice: Organizations are expected to implement technological controls that are appropriate to the level of risk and provide appropriate protection for systems, networks, and data, including the ability to detect, deter, and respond to security incidents.
ISO 27002:2022 vs 2013 (What Actually Changed)
If you're familiar with the older ISO 27002, you will find that the 2022 update introduces several key changes. The new version moves to a more flexible, attribute-driven model for classifying controls, which better aligns with modern security practices.
Area | ISO 27002:2013 | ISO 27002:2022 |
Total Controls | 114 | 93 |
Structure | 14 Domains | 4 Themes |
New Controls | N/A | 11 new controls added |
Attributes | None | 5 attribute types introduced |
So, what does this mean in practice?
The most significant change is the introduction of attributes. Attributes allow organizations to filter and view controls based on specific criteria, improving flexibility and usability.
Controls are now tagged with attributes like:
Control type: Preventive, detective, or corrective.
Security properties: Confidentiality, integrity, and availability.
Cybersecurity concepts: Identify, protect, detect, respond, and recover.
Moreover, the update introduced 11 new controls to meet contemporary requirements, such as cloud security, secure coding, and threat intelligence.
ISO 27002 Controls List (Quick Reference)
While the previous section explains how the four themes function, it is also useful to understand how controls are distributed across ISO 27002. The standard includes 93 controls, grouped as follows:
Organizational Controls (37): Example controls include 5.1 Policies for information security, 5.7 Threat intelligence, and 5.23 Information security for use of cloud services.
People Controls (8): Example controls include 6.1 Screening, 6.3 Information security awareness, education, and training, and 6.7 Remote working.
Physical Controls (14): Example controls include 7.1 Physical security perimeters, 7.4 Physical security monitoring, and 7.10 Storage media.
Technological Controls (34): Example controls include 8.9 Configuration management, 8.11 Data masking, and 8.28 Secure coding.
Important Note: These examples are illustrative, not exhaustive. You will select controls based on your risk assessment and document their applicability in a Statement of Applicability (SoA).
New ISO 27002 Controls You Should Not Ignore
The 2022 update of ISO 27002 added 11 new controls to deal with digital threats that are common today. These controls reflect emerging risk areas and are often considered during audit and risk evaluation processes. Organizations are expected to demonstrate how these controls are addressed as part of their risk management approach.
Some important new controls are:
5.7 Threat intelligence: Getting and analyzing information about new threats to help with proactive risk management.
5.23 Information security for use of cloud services: Dealing with the risks that come with using cloud services and shared responsibility models.
5.30 ICT readiness for business continuity: Making sure that systems and technologies can help with recovery and continuity goals.
7.4 Physical security monitoring: Improving the monitoring and surveillance of physical spaces.
8.9 Configuration management: Keeping system configurations safe and consistent.
8.10 Information deletion: Making sure that information is safely and completely deleted when it is no longer needed.
8.11 Data masking: Hiding sensitive data to keep it safe when full access isn't needed.
8.12 Data leakage prevention: Finding and stopping unauthorized data exfiltration.
8.16 Monitoring activities: Setting up logging and monitoring to find unusual behavior.
8.23 Web filtering: Controlling access to web content that could be harmful or inappropriate.
8.28 Secure coding: Putting security practices throughout the software development lifecycle.
How Auditors Evaluate ISO 27002 Controls
Understanding how auditors evaluate controls can help organizations prepare more effectively. Auditors usually check controls against certain standards:
Control design adequacy: Does the control genuinely aim to reduce the identified risk?
Implementation consistency: Is the control used consistently across the whole organization, or are there some exceptions?
Proof and audit trails: Can you show that the control is working through logs, reports, or other documents?
Risk alignment: Does the control directly link to a specific risk identified in the risk assessment?
Some common gaps in audits are:
Controls exist but are not operational: You have a great policy, but nobody follows it.
Weak documentation: You perform the process, but you cannot prove it to the auditor.
No mapping to risks: You implemented a control simply because it was in the standard, not because it addressed a real threat.
Characteristics of Effective Audit Evidence: Good evidence is time-stamped, clearly linked to a specific control, and demonstrates that a defined process was followed by an authorized person.
How Roz Supports ISO 27002 Engagements
Managing an ISO 27002 engagement manually can be complex. Roz is an AI-native engagement and audit-delivery platform that helps CPA firms and advisory teams structure documentation and audit workflows more effectively.
With Roz, teams can:
Centralize documentation by organizing policies, procedures, and evidence in secure, client-specific workspaces.
Generate AI-assisted draft workpapers with audit trails and source links.
Extract and map controls from uploaded documentation, supporting structured comparison against framework requirements.
Highlight potential gaps through first-pass analysis.
Roz does not replace auditors or certification bodies. Instead, it supports audit workflows by structuring documentation and assisting with first-pass analysis, helping reduce manual effort and improve consistency across engagements.
Conclusion
Adopting ISO 27002 is not just a compliance exercise; it is a structured approach to building resilience. By treating the standard as a practical guide for ISO 27001, you can shift from reactive security measures to proactive, risk-based management.
This framework forces you to identify control gaps, improve consistency, and enhance traceability between risks, controls, and evidence, fixing weaknesses before they become problems.