ISO 27001 vs SOC 2: Which Security Standard Fits Best?
If you are a SaaS founder, a CISO, or a compliance leader, you have probably looked at a vendor security questionnaire and felt your heart race. Enterprise customers don't just want to know if you're safe; they want proof. In the world of cybersecurity compliance, that proof is usually an acronym.
ISO 27001 and SOC 2 are the two biggest names in this field. To someone who doesn't know what they are, they might look like the same thing: costly, time-consuming audits that give you a badge to put on your website. But it is a strategic mistake to treat them as if they are the same. One is a widely used plan for managing risk, and the other is a thorough check of how your controls work in the real world.
If you pick the wrong one first, you could waste money, have longer sales cycles, and end up with a security program that doesn't really help your company. In this article, we will help you choose the framework that will help you grow the fastest and the one that you can put off using until later.
Are ISO 27001 and SOC 2 the same?
Unfortunately, no Although both ISO 27001 certification and SOC 2 attestation reports evaluate how the company collects and secures sensitive personal information, their answers differ.
Think of ISO 27001 and other certifications as blueprints to your house. They certify that you have a working system, or the ISMS that is built around the principle of “managing risk continuously.” They emphasize the importance of having the right tools to proactively prevent and/or mitigate issues and risks so they don’t escalate.
SOC 2 is like a house after construction. The house is there, and the systems are built, but the inspection does not determine how the house is built; it only examines the security controls, like whether the doors have working locks and whether the security system functions as it was designed. SOC 2 reports are not permanent and typically cover a defined reporting period, which is why companies usually obtain a new report annually.
Summary:
ISO 27001 - An international certification proving you have a structured, risk-based information security management system.
SOC 2 - A U.S.-focused attestation report verifying that your specific security controls are properly designed and operating effectively.
What is ISO 27001?
ISO 27001 is a globally recognized international standard for information security management, published by the International Organization for Standardization and the International Electrotechnical Commission.
Unlike other frameworks that focus heavily on specific technical rules, ISO 27001 is all about the Information Security Management System. The ISMS is a system of company policies, procedures, and all the legal, physical, and technical controls that relate to a company’s information risk management.
Key characteristics
Risk-Based Framework: You get to identify all the risks that are specific to your company, and then you implement controls to mitigate those risks. This is not a 'checkbox' type of exercise; it is a system that you manage.
Global Recognition: Across Europe, the Asia Pacific region, and many others, ISO 27001 is recognized and is a common requirement in global business contracts.
Certification Cycle: You are not done once you obtain certification. The cycle is 3 years. You start with a tough first audit (Stage 1 and Stage 2), then you will have an annual audit (also called a surveillance audit) to ensure you are compliant, and then you will have a recertification audit in year 3.
Annex A Controls: The standard has 93 updated controls divided into organizational, people, physical, and technological categories. The Statement of Applicability is a document in which companies present their selected controls and provide justifications for the inclusion and exclusion of Annex A controls, linked to their contextual risk.
What is SOC 2?
SOC 2 (System and Organization Controls 2) is one of the voluntary standards for service organizations created by the American Institute of Certified Public Accountants, and in most cases, U.S. enterprise customers will ask for these.
When it comes to the standard ISO 27001, the question is, “Do you have a system to manage security?” and for a SOC 2, the question is, “Are your security controls designed in such a way and (for Type 2) do they work over a span of time?”
The Trust Services Criteria
SOC 2 is built around five Trust Services Criteria. If you happen to be audited against these, you don’t have to be audited against all five; however, security is always a requirement.
Security (Common Criteria): The system is protected against unauthorized access.
Availability: The system is available for operation and use as committed or agreed.
Processing Integrity: System processing is complete, valid, accurate, timely, and authorized.
Confidentiality: Information designated as confidential is protected.
Privacy: Personal information is collected, used, retained, disclosed, and disposed of in conformity with the entity’s privacy notice.
Type 1 vs. Type 2
This is the most common point of confusion for founders.
SOC 2 Type 1: A Type 1 report looks at whether your security controls are appropriately designed and implemented as of a particular date. This means the report serves as a snapshot. The auditor makes no evaluation about whether the controls are designed adequately or whether they are effective. Type 1 reports are usually faster and cheaper. This is why many startups go for Type 1 as a way of trying to show some sort of security maturity while working toward Type 2.
SOC 2 Type 2: A Type 2 report looks at the design and the operational efficacy of your security controls at a particular time period, usually ranging from 6 to 12 months. This sort of report, while it takes a longer time, gives a greater level of assurance. This is because it means the auditor does not simply check whether your controls are designed adequately; they simply have to test whether those controls have acted effectively over a given time period. For large enterprise customers, a Type 2 report is probably the best you can get as it shows you are determined to have security protocols not just at one period of time.
ISO 27001 vs SOC 2: Key Differences Explained
The table shows the primary differences that will impact your timeline and budget.
Feature | ISO 27001 | SOC 2 |
Type | Certification | Attestation Report |
Primary Focus | Establishing and maintaining a risk-based ISMS | Evaluating the design and operating effectiveness of controls |
Primary Geography | International (Global standard) | Primarily U.S. standard |
Validity | 3-year certification cycle with surveillance audits | Covers a defined period (typically 6–12 months); buyers expect recent reports |
Output | A certificate (pass/fail) | A detailed audit report (opinion on effectiveness) |
Framework Basis | ISMS + Annex A Controls | Trust Services Criteria (TSC) |
Who performs it? | Accredited Certification Body | Licensed CPA Firm |
The "Pass/Fail" vs. "Opinion" difference
ISO 27001 certification means that the company has fulfilled the standard's requirements. If there are a couple of minor nonconformities, they can be fixed to achieve certification. The certificate is very high-level and does not speak to specific findings.
SOC 2, on the other hand, has a very specific and very long report (usually greater than 100 pages). The report has the opinion of the auditor, and that is, if it is an unrestricted opinion, that means controls were properly designed and operated; a restricted opinion means there are issues, and an adverse opinion means there are lots of issues. Because SOC 2 reports are so specific, they can be sent to potential clients only if there is an NDA in place.
ISO 27001 vs SOC 2 Cost Comparison
Estimating budgeting for an ISO 27001 or SOC 2 report is difficult because there is more to consider than the audit itself. There will be internal costs for preparation, tools, and time to create evidence that the operational and engineering teams will spend sifting through countless items for the audit.
Important Note: Cost estimates for both ISO 27001 and SOC 2 mentioned here vary based on scope, geography, auditor selection, and internal readiness. You should obtain tailored quotes for accurate budgeting.
ISO 27001 Costs
ISO 27001 generally has higher upfront effort and cost requirements at the start since an entire ISMS has to be built and used to be able to get the audit for some controls.
Audit Fees: Certification audits are split into 2 stages: Stage 1 is the document review, and Stage 2 is the implementation audit. Many companies pay $10k to $20k for these stages with a certification body. For larger companies, audit and certification costs can go up to $50k, $200k, or more, depending on the scope, size, and complexity of the implementation. These costs are charged by accredited certification bodies, and preparation costs are separate.
Surveillance Audits: In years 2 and 3, you pay for smaller surveillance audits, which usually cost about 50-60% of the initial audit fee.
Preparation: Without automation, implementation can take anywhere from 6 to 12 months. This means you may need to pay external consultants ($20k+) or hire new employees to manage the documentation.
SOC 2 Costs
SOC 2 costs vary based on how well you are prepared, your company's size, and whether you get a Type 1 or Type 2 report.
Audit Fees:
Type 1: Generally between from $5k to $25k.
Type 2: Generally between from $30k to $80k.
Preparation: If you hire a consultant, the readiness assessments and gap analyses can cost an additional $5k-$15k.
Hidden Costs: The largest SOC 2 cost driver is often internal labor. Before the audits can start, you need to gap assess and operationalize your controls. This often means working with engineering and operations to gather evidence and assess readiness, and then to do that again during the formal audit testing. Without a well-structured procedure, collecting evidence can overly complicate the audit prep process. If you do not invest in automation, your engineering team will spend significant hours on evidence collection, security and compliance work, and operational documentation. The time costs can be much higher than the costs of the audit, which is typically 10-30% of your total investment.
Control Overlap: Can One Help You Achieve the Other?
ISO 27001 and SOC 2 controls have a lot in common. However, meeting one framework does not automatically mean that the other is met, especially because ISO 27001 has more ISMS governance and ongoing improvement requirements.
An alignment of controls across ISO 27001 Annex A and the SOC 2 Trust Services Criteria, particularly for the Security (Common Criteria) one, is common for many companies.
If You Already Have SOC 2
If your company almost certainly has SOC 2 (especially Type 2), which means you have already implemented controls for:
Access management
Change management
Data backup and recovery
Vendor risk management
Incident response
Monitoring and logging
All these controls satisfy the requirements of ISO 27001. The biggest gap when moving up to ISO 27001 is putting in place a governance structure, which is the ISMS. This comprises documentation of risk management processes, Statement of Applicability, internal audits, management review meetings, and evidence of continual improvement. SOC 2 is all about controls, whereas ISO 27001 is more about the management system around the controls.
If You Are ISO 27001 Certified
With your ISO 27001 certification, you already have a formal ISMS in place and have integrated security governance into your company. To achieve SOC 2, you will need to:
Map your existing controls to the SOC 2 Trust Services Criteria
Undergo a CPA-led attestation
Show control effectiveness over a reporting period
Show proof in line with SOC 2 audit standards
ISO 27001 certification makes the process to SOC 2 easier. It is important to note that the SOC 2 process has its own independent attestation and testing methodology.
Which Should You Choose First?
If you have unlimited budget and time, do both. But you will need to make a decision based on the immediate needs of the company. Here is a decision framework to help you choose.
Choose SOC 2 First If:
Your primary market is North America: Many enterprise buyers in the U.S. request SOC 2 as a standard for security compliance. Even if you hold an ISO 27001 certification, they may still require a SOC 2 report.
You need speed. SOC 2 Type 1 can often be achieved faster than ISO 27001, sometimes in a few months, depending on readiness, while ISO 27001 will take significantly longer because of its Stage 1/Stage 2 audit.
You are a B2B SaaS company. In the U.S. SaaS industry, SOC 2 is an essential trust signal and is seen as a bare minimum requirement to win vendor approval from enterprise and mid-market procurement teams.
Choose ISO 27001 First If:
You are expanding internationally - If you are trying to enter Europe, Japan, or Australia, ISO 27001 is a widely recognized international benchmark for information security management.
You are in a highly regulated sector - When it comes to finance, healthcare, and government contracting, ISO 27001 is preferred due to the formal structure and governance that comes with an ISMS.
You want a structured security program - If you want to construct a security culture from scratch instead of simply “passing an audit,” the ISMS framework of ISO 27001 compels you to build long-term habits for the future.
When You Might Need Both
For fast-growing companies, the question is not whether you'll need both SOC 2 and ISO 27001, but rather when. You could begin with SOC 2 to secure U.S. customers, but a potential customer in Europe will request ISO 27001. Or, you could be getting ready for an IPO, and both governance (ISO) and operational evidence (SOC 2) are going to be reviewed.
It may feel overwhelming to run both programs simultaneously, but it's the most effective way to go. There is a lot of control overlap, and adding one framework on top of another is easier than starting with a blank slate. The first rule of thumb is to maintain only one set of policies and evidence and map your controls to both frameworks so you don’t duplicate your efforts. When done correctly, one program can be used to efficientlysupport the other.
Conclusion
ISO 27001 and SOC 2 are not competitors; they are two tools to earn trust building renewals. ISO 27001 shows that you can manage risk, and SOC 2 shows that your controls are effective.
Your growth strategy will dictate the next steps. If you need to clear U.S. sales revenue this quarter, SOC 2 is probably the best option. If you need to establish a global foundation for the next decade, ISO 27001 is the blueprint you need.
No matter what you decide, the goal is not the badge; it’s about creating a company that customers can trust. The audit is just the proof.
Join Roz and Deliver Smarter Audits
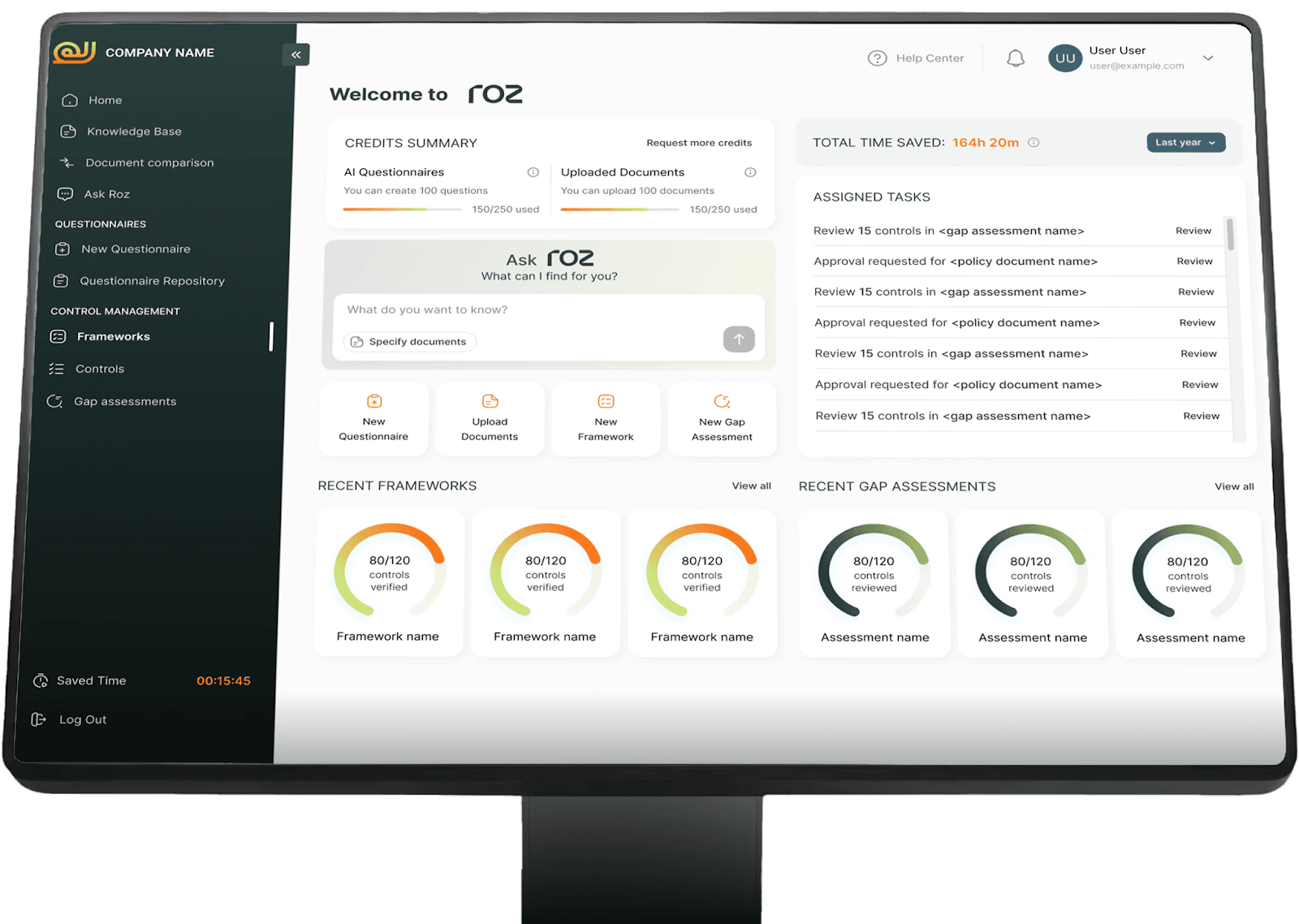
This is your chance if you run a modern audit, risk assurance, or advisory company and want to grow quickly.
Roz helps companies standardize how they deliver engagements, automate first-pass analysis, and create structured workpapers with full audit trails. This cuts down on manual work and makes audits more defensible.
Your team can spend less time on drafting and reviewing documents that are the same over and over again and more time on high-impact analyzis and client advisory.
We offer AI workpaper generation, structured control testing, gap analysis, and centralized engagement workspaces. These tools are meant to help companies become more consistent, make more money, and grow with confidence.
Are you ready to bring your company's audits up to date?
Frequently Asked Questions
Which is faster to get?
SOC 2 Type 1 is usually faster. ISO 27001 typically takes longer due to the fact that ISMS implementation is a requirement.
Is SOC 2 recognized outside the U.S.?
Yes, although it is most frequently requested by U.S.-based companies. On the other hand, ISO 27001 is recognized for its wider reach.
Does ISO 27001 require all 93 Annex A controls?
No. It is up to the company to determine which controls apply to them based on their risk analyzis.