SOC 1 vs SOC 2: Key Differences Explained
Feb 24, 2026

Do you know which SOC report customers are asking for? Many companies struggle with the differences between SOC 1 and SOC 2, but the consequence of selecting the wrong one is the loss of several months of work and thousands of dollars.
The difference is simple: SOC 1 covers controls relevant to financial reporting, and SOC 2 covers controls for security, availability, processing integrity, confidentiality, and privacy.
This is different because every report treats different risks and addresses different stakeholder concerns. If your service has a direct impact on your customers’ financial statements, like payroll, invoicing, or claims processing, then you are likely to require SOC 1. When you provide a service that involves the storage of the customer’s sensitive data through SaaS, cloud infrastructure, or customer hosting, then SOC 2 is likely to apply.
In this article, I will break down what has to be included in the report, who will need a report, the differences in cost and scope, and how to identify the best position for your company.
What Is SOC 1?
SOC 1 reports focus on the relevant services provided by a service organization that may impact the user entities' internal control over financial reporting. As per the American Institute of Certified Public Accountants, SOC 1 reports should focus on the specific needs of service organization users and the user entities' financial statement auditors.
SOC 1 reports are one of the types of reports that can be completed under the SSAE 18 AT-C Section 320 guidelines, providing evidence of the controls your organization has put in place with respect to the reporting of your customers' financial information.
Who Needs SOC 1?
SOC 1 is a necessity for companies that provide services that affect the customer’s financial statements. Examples of these types of services are:
Payroll companies that process and calculate the payment of employees, taxes, and other withholdings.
Billing systems that generate invoices and take payments.
Financial reporting systems that capture and record accounting transactions.
Claims processing systems that process payments for insured individuals.
Loan servicing companies that process and report on payments.
SOC 1 is likely the framework you need if customer auditors have to rely on your controls for the financial statement audits.
SOC 1 Control Objectives
SOC 1 control objectives typically fall into two categories:
General IT Controls:
Logical access controls.
Physical access controls.
Systems security management and monitoring.
Change management procedures.
Backup and recovery processes.
Business Processing Controls:
Transaction input and processing accuracy.
File processing completeness.
Information reporting integrity.
Legal and liability management.
Unlike SOC 2, which has set criteria based on the Trust Services Criteria, companies have the flexibility with SOC 1 to determine control objectives based on the nature of the services offered and their relevance to the financial reporting.
What Is SOC 2?
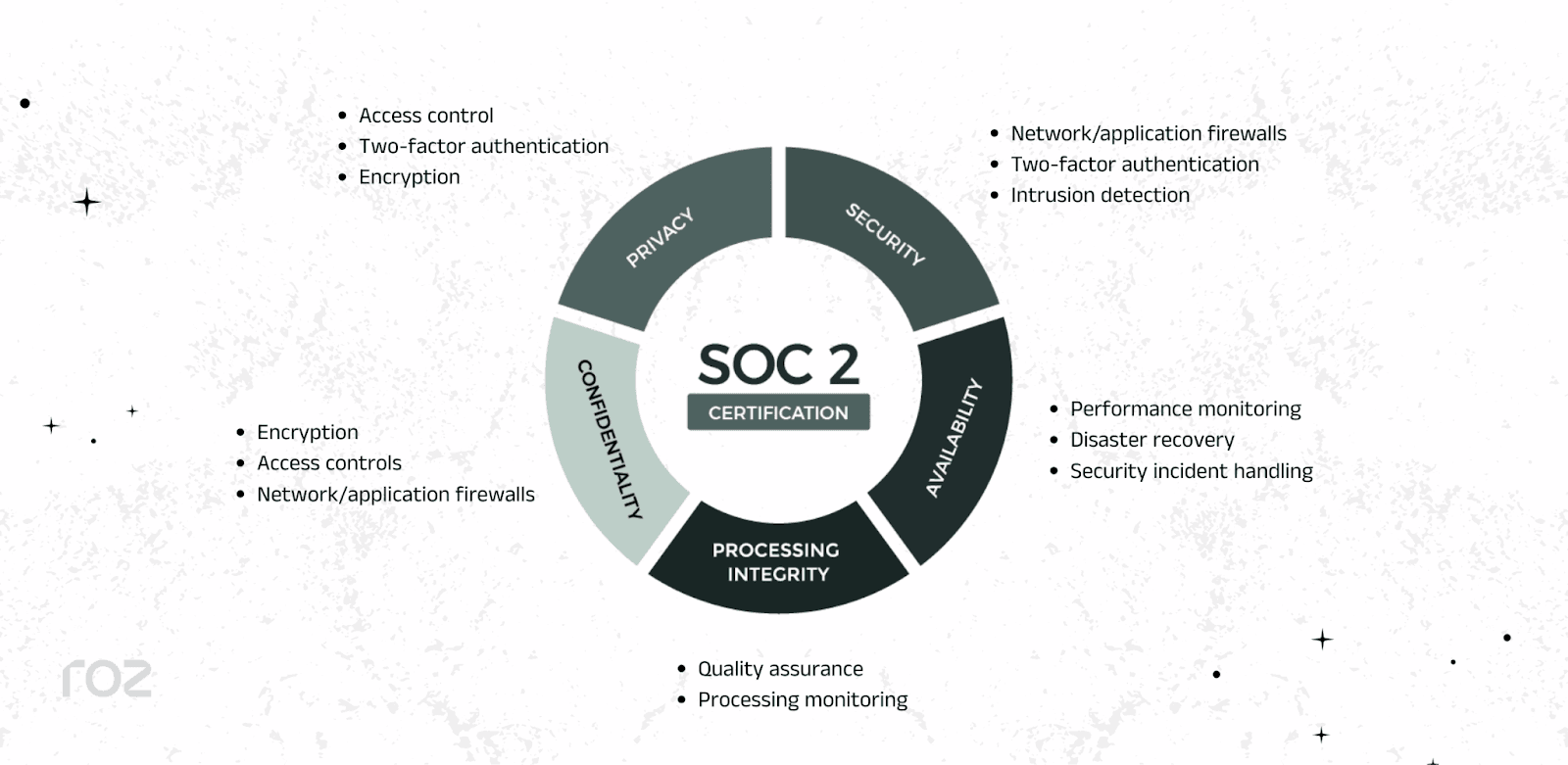
SOC 2 represents an audit of a service company’s controls from the perspective of the AICPA’s Trust Services Criteria. This perspective focuses on how companies construct their governance structures and the processes that protect and secure customer data. Such processes are evaluated according to the criteria of security, availability, processing integrity, confidentiality, and the privacy of data.
SOC 2 reports are governed by SSAE 18 AT-C Section 105 and SSAE 21 AT-C 205. These reports relate to a professional service company that uses technology and cloud-based service providers to store, process, or transmit customer data.
Who Needs SOC 2?
SOC 2 is a requirement for companies that are processing sensitive customer information, which does not necessarily have a direct impact on financial reporting. Such companies include:
Data centers that store customer data.
SaaS solution providers that provide business applications.
Cloud service companies that provide customer infrastructure.
Managed IT service providers that manage customer systems.
Health technology systems that process protected health information.
HR and recruitment systems that handle employee data.
When customers ask questions about your company’s security, data protection, or compliance with privacy regulations, they're likely looking for SOC 2.
SOC 2 Trust Services Criteria
According to the AICPA's 2017 Trust Services Criteria, SOC 2 considers 5 categories. Security is the only criterion that is mandatory for every audit.
Security (Common Criteria): Protection is provided against unauthorized access, disclosure, and destruction.
Availability: Systems are operational and available as committed or agreed.
Processing Integrity: Processing of the system is complete, valid, accurate, timely, and authorized.
Confidentiality: Confidential data is secured through access controls and other means.
Privacy: Personal data is processed per the company’s privacy notice, including proper collection, use, and disposal.
You can choose additional criteria based on their services and customer needs.
SOC 1 vs SOC 2 Comparison
Factor | SOC 1 | SOC 2 |
Primary Focus | Internal controls over financial reporting (ICFR) | Data Security and Trust Services Criteria |
Control Framework | Organization-defined control objectives | AICPA Trust Services Criteria (Security mandatory; Availability, Processing Integrity, Confidentiality, Privacy optional) |
Intended Audience | Financial auditors, CFOs, and finance teams | Security teams, compliance officers, risk managers, and customers |
AICPA Standard | SSAE 18 AT-C 320 | SSAE 18 AT-C 105 and SSAE 21 AT-C 205 |
Typical Industries | Payroll processing, billing platforms, financial software, and claims processing | SaaS, cloud providers, data centers, and IT managed services |
Report Distribution | Restricted (user entities and their auditors) | Restricted (customers and stakeholders under NDA) |
Type 1 Focus | Design of financial reporting controls at a point in time | Design of security and trust controls at a point in time |
Type 2 Focus | Operating effectiveness of financial reporting controls over 3-12 months | Operating effectiveness of security and trust controls over 3-12 months |
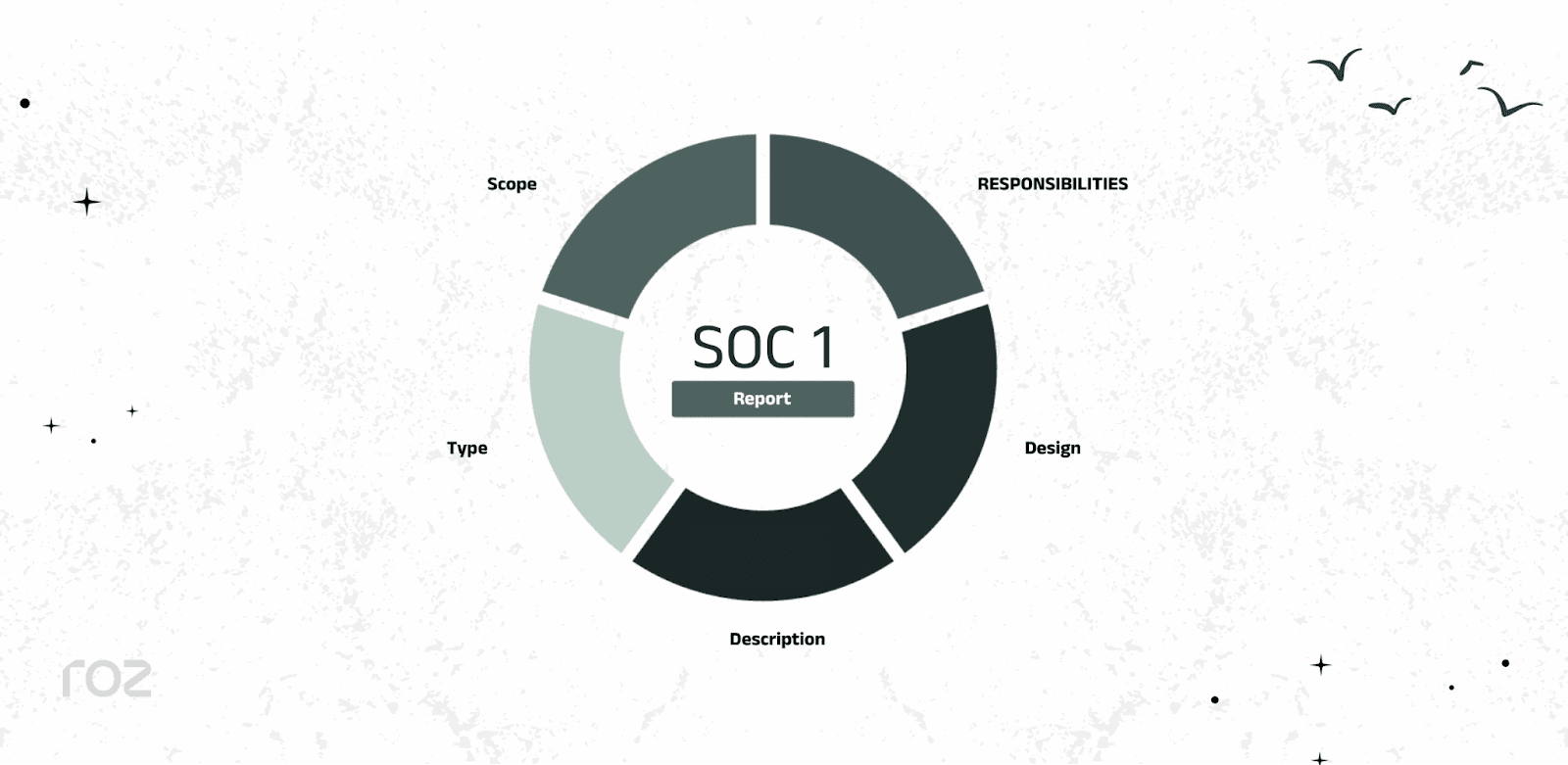
Understanding Type 1 vs Type 2 Reports
When it comes to SOC 1 and SOC 2 examinations, there are two types of reports for each, and they differ by scope and depth of testing approaches.
Type 1 Reports
A Type 1 Reports are evaluated based on whether the company's controls are designed and implemented reliably as of a particular date. It only describes whether the control environment is implemented and does not include an evaluation of whether the control environment is implemented.
What Type 1 Includes:
System description
Control descriptions
Management’s assertion
Auditor’s opinion on design suitability
Timeline: Type 1 reports usually take 4-8 weeks once controls and documentation are completed.
Best For: Companies that want to show implemented control design to fulfill requirements imposed by a vendor, or start their compliance journey before getting a Type 2 report.
Type 2 Reports
A Type 2 report considers both the design and operational efficacy of controls over the specified time frame; it usually takes 6-12 months. Instead of a snapshot, this report gives assurance that controls remain in place and function over time.
What Type 2 Includes:
Everything in a Type 1 report, plus:
More detailed testing procedures.
Results of control testing.
Proof of control operation over the reporting period.
Identification of exceptions or deviations.
Timeline: Type 2 Reports have 6-month initial engagement observation periods followed by 4-8 weeks of reporting and testing by the auditor.
Best For: Companies wanting to show high control maturity and consistent operation to enterprise customers, regulators, and high-trust stakeholders.
Most enterprise buyers have shown to require Type 2 reports most often as they offer far more assurance than Type 1 reports about the effectiveness of ongoing control.
SOC 1 vs SOC 2: Which One Do You Need?
The right SOC report is based on how your services are used by your customers and whether you impact their financial reporting or their data security posture.
Choose SOC 1 If You:
Provide services that impact customer financial statements.
Process payroll or employee benefits.
Create invoices or manage financial reporting.
Perform loan servicing or payment processing.
Manage financial reporting systems.
Have customers whose auditors depend on your controls.
Example Scenario: You run a payroll platform that processes wage calculations, tax withholdings, and benefit deductions for several companies. Your processing directly affects your customers' financial statements, so this is an SOC 1 situation.
Choose SOC 2 If You:
Store or process sensitive customer data.
Provide cloud-based services or SaaS applications.
Run data centers or provide hosting services.
Provide managed IT services.
Handle healthcare, HR, or personal information.
Face security questionnaires from enterprise customers.
Example Scenario: If you are a cloud-based project management software, you are likely to have customers who store sensitive documents, messages, and data related to their projects. Such customers are likely to have strict security, confidentiality, and availability requirements, and that makes this an SOC 2 situation.
Note: Most requirements for SOC 2 are driven by customers and the market, instead of a legal requirement.
What If You Need Both?
Some companies require both SOC 1 and SOC 2 reports to meet their customers' varied risk requirements. For example, a cloud accounting platform may need SOC 1 (to cover financial reporting impacts) and SOC 2 (to cover data loss concerns). Similarly, an HR technology provider may need SOC 1 (for payroll processing) and SOC 2 (to cover employee data).
Although their purposes are not the same, overlapping concerns regarding shared IT controls, such as access and change management, and so on, may exist. Performing both audits at the same time may simplify the testing and improve the overall process.
Cost & Timeline Comparison
When a company starts to understand the difference in cost for SOC 1 vs SOC 2, it helps with better company planning.
SOC 2 Costs
SOC 2 engagements usually require more extensive coordination across the company, especially when multiple Trust Services Criteria are involved:
SOC 2 Type 1:
- Estimated total investment: $20,000-$50,000
Type 1 looks at a control's design at one moment in time, limiting the time involved, as well as the testing requirements.
SOC 2 Type 2:
- Estimated total investment: $40,000-$100,000+
Type 2 has a longer time frame (6-12 months) because they have testing the control's effectiveness. This means that the company has to prove that the control has been working effectively for an extended period, resulting in more preparation and documentation.
SOC 1 Costs
SOC 1 focuses more on controls that relate to financial reporting. Because of this, costs are often similar to SOC 2, but they might also be lower or higher depending on the nature of the transactions and the level of complexity in the system design.
SOC 1 Type 1:
- Estimated total investment: $20,000-$40,000
SOC 1 Type 2:
- Estimated total investment: $35,000-$90,000+
Although SOC 1 is more narrow in scope than SOC 2, companies with high transaction volumes or complex financial processing may incur similar costs.
Hidden Costs to Consider
Apart from the audit fees, you need to budget for:
Preparation Costs:
Gap assessments or readiness reviews.
Policy drafting and documentation updates.
Control remediation efforts.
Security tooling or infrastructure improvements.
Ongoing Costs:
Annual renewal audits.
Continuous compliance monitoring tools.
Internal compliance team time.
Penetration testing (usually $5,000-$20,000 depending on scope).
Periodic risk assessments.
Important Note: Most of the figures stated above are general estimates for small to mid-sized companies. Your actual costs will differ based on your company’s size, complexity, location, and the auditor you decide to work with. Because SOC reports are offered by licensed CPA firms, there is no pricing uniformity in the industry.
Common Mistakes Companies Make
1. Choosing the Wrong Report Type
A common mistake is going for an SOC 2 report when they actually need an SOC 1 report or vice versa. This happens when a client requests a general SOC report. You can avoid this mistake by identifying whether the report is supposed to focus on financial controls (SOC 1) or data security (SOC 2) from the beginning. This saves both time and costs.
2. Underestimating Type 2 Evidence Needs
Type 2 report first timers think they need less evidence than what is actually required. This is logical, as a Type 1 is a snapshot in time, but a Type 2 is looking for evidence that the control(s) functioned effectively for a 6-12 month period. In the absence of documentation that is consistent, there will be substantial gaps and delays. Before a readiness assessment, the absence of a strong plan for capturing ongoing evidence will constitute a failure.
3. Treating Compliance as a One-Time Project
You have to renew SOC reports every year. This is why compliance cannot be left just like that for the period until the next audit. Non-renewable controls can make the next audit very difficult. Compliance is about control, monitoring, and operational processes. It is not an audit season activity.
4. Poor Documentation Practices
Great controls can't save you from an audit if your documentation is poor. Approved missing documentation, unrecorded changes, and reviews that leave documents uncompleted are common problems. The audit's outcome is often highly correlated with the quality of documentation. Streamlining your documentation practices from the start is a good way to ensure a less painful experience.
5. Neglecting Workpaper Management
Auditors are looking for evidence that they can follow. When documentation is all over the place and is scattered across shared drives, spreadsheets, and emails, the audit will be unnecessarily dragged out. Disorganization creates delays and version control issues. Strengthening your audit trail and centralizing your evidence will create greater efficiency.
How Roz Supports SOC 1 and SOC 2 Engagements
SOC examinations require detailed documentation, traceability, and streamlined processes. We are an AI-native audit-delivery platform built for CPA, risk assurance, and advisory teams performing SOC 1 and SOC 2 engagements.
Our tool supports engagement teams by automating first-pass analyses, organizing documentation, and ensuring consistency across engagements.
What Roz Enables
Customer-specific workspaces to centralize policies, evidence, and workpapers.
AI-generated draft workpapers with complete audit trails and link sourcing.
Control extraction and mapping to SOC objectives or Trust Services Criteria.
Structured gap analysis before detailed testing.
First-pass control testing and evidence sufficiency checks.
For SOC 1: Our tool helps in organizing ICFR documentation, mapping financial controls to pieces of evidence, and streamlining the workpapers review process.
For SOC 2: Our tool helps in mapping evidence to Trust Services Criteria, further organizing documentation according to the respective criterion, and enhancing workflows for first-pass testing.
By replacing spreadsheets and email chains with an AI-assisted engagement structure, Roz helps companies deliver SOC engagements more efficiently, without compromising audit rigor. auditor oversight.
Conclusion
When choosing between SOC 1 and SOC 2, ask yourself one simple question: Does your service impact a customer’s financial reporting or their data security?
Choose SOC 1 for services that impact your customers’ financial statements.
Choose SOC 2 for services that protect confidential data and sustain operational consistency.
In some situations, you might need to get both.
Regardless of which report is chosen, significant planning and ongoing management of your controls are essential. Hopefully, this guide has provided you with enough information to make the right decision for your company.